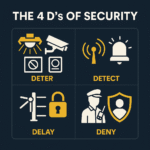
 Protecting your property, assets, and people requires a layered approach. It’s not enough to simply react to threats as they happen; an effective security strategy is proactive and multifaceted. Security professionals often use a framework known as the 4 Ds of Security to build a robust defence system. This concept breaks down security into four key stages: Deter, Detect, Delay, and Deny.
Protecting your property, assets, and people requires a layered approach. It’s not enough to simply react to threats as they happen; an effective security strategy is proactive and multifaceted. Security professionals often use a framework known as the 4 Ds of Security to build a robust defence system. This concept breaks down security into four key stages: Deter, Detect, Delay, and Deny.
Understanding these four principles is fundamental to creating a security plan that anticipates and mitigates risks before they escalate. By integrating measures that address each of these stages, you can create a comprehensive shield around what matters most. This guide will walk you through each of the 4 Ds, explaining what they mean and how they work together to protect your premises.
1. Deter: The First Line of Defence
The first ‘D’ stands for Deter, which is all about preventing a threat from occurring in the first place. The primary goal is to make your property an unattractive target for potential intruders or criminals. Deterrence works by creating the perception that any attempt to breach security will be difficult, and the risk of getting caught is high. It’s a psychological barrier that discourages wrongful activity before it even begins.
Effective deterrence is often highly visible. The mere presence of security measures can be enough to make a potential offender think twice.
Examples of Deterrence:
- Visible Security Personnel: A uniformed security guard patrolling the premises or stationed at an entrance sends a powerful message that the site is actively monitored. Their professional presence is one of the most effective deterrents.
- Surveillance Systems: Prominently placed CCTV cameras and clear signage indicating that the area is under surveillance act as a constant reminder that actions are being recorded.
- Access Control Systems: Gates, turnstiles, and visible card readers at entry points signal that access is restricted and controlled, discouraging unauthorised individuals from trying to enter.
2. Detect: Identifying a Breach
The second ‘D’ is Detect. If deterrence fails and an intruder attempts to breach your security, the next layer of defence is to identify this activity as quickly as possible. The goal of detection is to provide early and accurate warnings of a security event, allowing for a swift and effective response. The sooner a breach is detected, the more time your security team or law enforcement has to react and minimise potential damage.
Detection systems are the “eyes and ears” of your security plan, alerting you to unauthorised access or suspicious behaviour.
Examples of Detection:
- Intrusion Alarms: Motion sensors, door and window contacts, and glass-break detectors trigger an alarm when unauthorised activity is identified, immediately notifying security personnel or a monitoring centre.
- Security Patrols: Trained guards conducting regular patrols are skilled at spotting unusual behaviour, signs of forced entry, or other potential threats that automated systems might miss.
- CCTV Monitoring: While cameras are a deterrent, they are also a crucial detection tool. When actively monitored, they provide real-time visuals of an incident, allowing for immediate verification and response.
3. Delay: Slowing Down the Threat
Once a threat has been detected, the third ‘D’, Delay, comes into play. The objective here is to slow down the intruder’s progress, creating a critical time window between detection and the intruder reaching their target. This delay gives your response team valuable time to arrive on the scene and intervene. Every second gained can make a significant difference in the outcome of a security incident.
Delay tactics are physical or procedural obstacles designed to impede an intruder’s movement.
Examples of Delay:
- Physical Barriers: Fences, gates, and bollards force an intruder to spend extra time trying to bypass them. These barriers should be robust enough to withstand attempts to break through them quickly.
- Reinforced Entry Points: Using reinforced doors, high-security locks, and shatter-resistant windows makes forced entry more difficult and time-consuming.
- Controlled Access Points: Implementing procedures like ID checks or multi-factor authentication at internal doors adds layers of security that slow down an intruder even after they have breached the perimeter.
4. Deny/Defend: The Final Stand
The final ‘D’ can be interpreted as Deny or Defend. This stage is the ultimate goal of your security system: preventing an intruder from successfully accessing your most valuable assets or sensitive areas. If all other layers have been breached, this is the final opportunity to stop the threat.
Deny focuses on making critical areas completely inaccessible to unauthorised individuals. This is often achieved through robust access control and physical security measures. Defend refers to the active response to a threat, usually carried out by trained security personnel.
Examples of Denial and Defence:
- Secure Storage: Using safes, vaults, or secure rooms with advanced locking mechanisms to store high-value assets or confidential information.
- Trained Security Personnel: A well-trained security force is essential for an active defence. Their skills in conflict resolution and emergency response can neutralise a threat and protect individuals on-site.
- Lockdown Procedures: Having clear and practised emergency protocols for lockdowns can effectively deny an intruder access to populated areas, ensuring the safety of employees and visitors.
Building a Layered Security Strategy
The 4 Ds of Security—Deter, Detect, Delay, and Deny/Defend—provide a powerful framework for building a comprehensive security plan. These principles work together, creating multiple layers of protection. A strong deterrent may prevent most incidents, but a reliable detection system is crucial for the few that aren’t. Should a breach occur, delay tactics buy the time needed for a successful defence.
For further reading on the effectiveness of layered security, refer to the U.S. Department of Homeland Security’s Physical Security Guidance and the ASIS International Physical Security Principles.
By thoughtfully implementing strategies for each of the 4 Ds, you can significantly enhance the safety of your property and create a secure environment for everyone. For specific strategies related to deterrence and detection, review insights from The Security Journal and best practices compiled by Interstate Security Inc..
